Space Hacking Odyssey
Hands-on satellite hacking training delivered at Black Hat and privately for mission teams.
Most security leaders assume space systems are just another critical infrastructure problem with higher latency and worse patch cycles.
They're not.
Space vehicles are designed with mission continuity as the first priority. Security is layered in carefully because the wrong control can degrade flight operations. That single constraint changes everything about how you model risk, persistence, and detection.
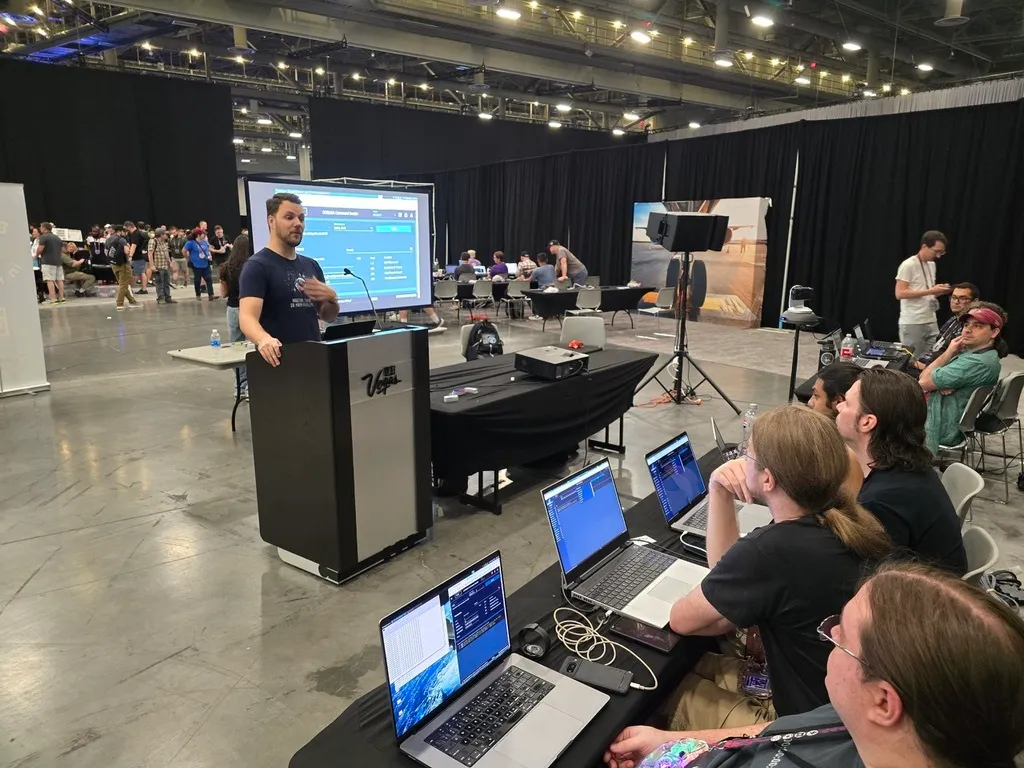
In this workshop — the same training we have delivered at Black Hat and other conferences — operators don't start with an exploit. They start by flying a simulated satellite.
Each participant runs a three-system environment: an operator console with orbital visualization, a ground station, and a satellite simulator using NASA's open flight software. Commands executed on the ground propagate to the spacecraft in real time. Only after understanding nominal operations do we introduce adversarial tradecraft mapped to SPARTA, culminating in uploading a custom flight software module that behaves like a covert backdoor.
If your team can't distinguish between a legitimate command sequence and a malicious one during a pass window, no amount of network monitoring will help.
Mission Environment
Each participant receives a complete mission environment:
Operator workstation
with orbital visualization
Ground station software
for command and telemetry
Satellite simulator
running NASA open flight software
Students begin by flying the satellite and learning normal mission operations. Only after understanding how the system behaves do we introduce adversarial tradecraft.
Labs progress through increasingly sophisticated attacks until participants are modifying flight software and deploying a covert backdoor module on the spacecraft.
What Participants Do
During the course, students will:
- Operate a simulated satellite mission environment
- Execute command sequences through a ground station
- Abuse mission operations workflows
- Intercept and manipulate command traffic
- Hide malicious activity in operational telemetry
- Map attacks using the SPARTA space threat framework
The progression builds from understanding to exploitation — each step grounded in how real mission operations work.
The question isn't whether your space systems have vulnerabilities. It's whether your operators would recognize an attack that looks like normal operations.
Why It's Different
Space cybersecurity is constrained by physics and mission operations.
Bandwidth is limited. Connectivity is intermittent. Patching is often impossible. The wrong defensive control can degrade flight operations.
Meaningful security testing requires understanding how operators, spacecraft software, and mission constraints interact. This course focuses on that reality rather than abstract vulnerability theory.

Industry Perspective
The course combines technical labs with strategic context about the space security ecosystem, including:
- How commercial and government programs approach mission security
- Emerging detection and monitoring approaches for spacecraft
- Real-world attack paths against ground and space segments
Guest lectures frequently include experts from organizations such as The Aerospace Corporation and Cal Poly's space cybersecurity program, along with other leaders in the field.

Where We Teach
Conference
We regularly teach this course at Black Hat and other major conferences.

Private Training
In addition to conference delivery, FFS provides this training privately for:
- Satellite operators and mission teams
- Space system integrators
- Security teams supporting space programs
Private sessions can emphasize either technical engineering depth or defensive strategy for leadership and security teams.

Bring It to Your Organization
If you are interested in hosting the course at a conference or running it privately for your organization, contact FFS to discuss availability.